
The zero-day market: discover, sell and keep quiet
Inside zero-day trade: brokers, prices, sanctions and leaked tools hitting phones and crypto.
For years cyberweapons for espionage were thought to be the preserve of a narrow circle of intelligence services. But a US government investigation into Operation Zero has exposed the scale of the zero-day trade. Two markets now surround exploits: one with brokers, price lists and suppliers; and a second where hackerware ends up after leaks or deliberate dumps.
What skimping on intelligence can cost, how much states will pay to crack a smartphone, and how to trust researchers who surface bugs decades on—the answers are in ForkLog’s new report.
The players
A zero-day vulnerability is a critical flaw in software or hardware used by hackers before the developer learns of it and ships a fix (a patch). The name hints that creators have zero days to eliminate the threat.
Demand centres not on the bug itself but on the “window of opportunity”—the guaranteed period of covert access before detection.
The 0-day market features three sets of participants:
- The cybersecurity researcher. An individual or team that finds a vulnerability.
- The broker. Intermediary firms that buy exploits and refine them into ready-to-use commercial products (infection chains) for resale.
- The customer. Intelligence and military agencies that want turnkey spying tools—cheaper and safer than recruiting human agents on the ground.
On the edge of legality
This market long sat in a grey zone, but recent events have shed light on its true scale. In February 2026 the US Treasury and State Department imposed sanctions on the Russian firm “Matrica” (the Operation Zero brand) and its founder, Sergey Zelenyuk.
The organisation openly styled itself as a cyberweapons broker. According to materials from the Treasury’s Office of Foreign Assets Control (OFAC), Operation Zero’s cardinal rule was to sell tools to clients outside NATO, in particular to state intelligence bodies.
The case hinged on an Operation Zero supplier who stole accesses from a US defence contractor (reportedly L3Harris). From 2022 to 2025 the Australian freelancer Peter Williams pilfered eight 0-day exploits built for intelligence use. He sold them for $1.3m in cryptocurrency.
This was not the first deployment of cyberweapons against US citizens, but it broke the market’s unwritten rules. While others tried to balance in the grey zone of “national security”, Operation Zero chose open confrontation with NATO.
Previously, OFAC’s sanctions list tended to catch malware developers only after high-profile scandals:
- 2021 — restrictions hit Israel’s NSO Group, creator of Pegasus, which was used to spy on diplomats, journalists and dissidents;
- 2024 — for aiding repression and surveillance, sanctions were imposed on the makers of the Predator spyware, Intellexa and Cytrox (Europe, Middle East).
Defining a cyberweapons seller’s legality is slippery. The market of official or semi-official (grey) outfits is fiercely competitive, with clear leaders such as the UAE’s Crowdfense. That firm has managed to avoid OFAC lists for several reasons:
- jurisdiction and export control. Crowdfense is registered in a country with partner ties to the US and its allies. Its leadership says it adheres to strict export-control and compliance rules. The transfer of cyberweapons is regulated much like the trade in conventional arms;
- choice of customers. Clients include the Five Eyes, as well as allied governments and law-enforcement bodies. For the US, Crowdfense is a lawful contractor supplying weaponry;
- legalisation. Crowdfense presents itself as a national-security instrument. When buying a vulnerability, it signs an NDA with the hacker and passes the exploit, say, to security services for tracking terrorists. Legally, that is procurement of special equipment.
Yet this “white zone” is conditional. In practice, a legal player’s status lasts only until its tools are swept up in a public scandal—especially if they enable surveillance of journalists or politicians in Western countries.
The price list
This section is for information of public interest only. The ForkLog editorial team condemns cybercrime and all forms of violence.
Zerodium was the first to haul zero-day trading out of the dark web into the open—formally lawful—arena. Founded in 2015 by cybersecurity researcher Chaouki Bekrar, the firm began publishing public price lists for buying exploits.
The company then refined the purchased accesses and resold them to a small circle of vetted clients—chiefly state intelligence services and law-enforcement agencies in NATO countries.
By the mid-2020s, however, that model had lost its edge. Pressure rose from two directions. On one side came new entrants with substantially deeper pockets, notably Dubai-based Crowdfense. On the other came faster update cycles at Apple and Google: exploit shelf lives shrank and broker risks grew.
Against this backdrop Zerodium’s top payout—about $2.5m—ceased to look attractive. The market quickly shifted to more aggressive pricing. Crowdfense effectively set a new marker: complex exploitation chains neared $10m, and in 2024 the company allocated $30m to an exploit-acquisition programme.
Today the hottest commodity remains a trace-free, zero-click smartphone compromise. At the time of writing the broker offers up to $7m for iOS and up to $5m for Android.
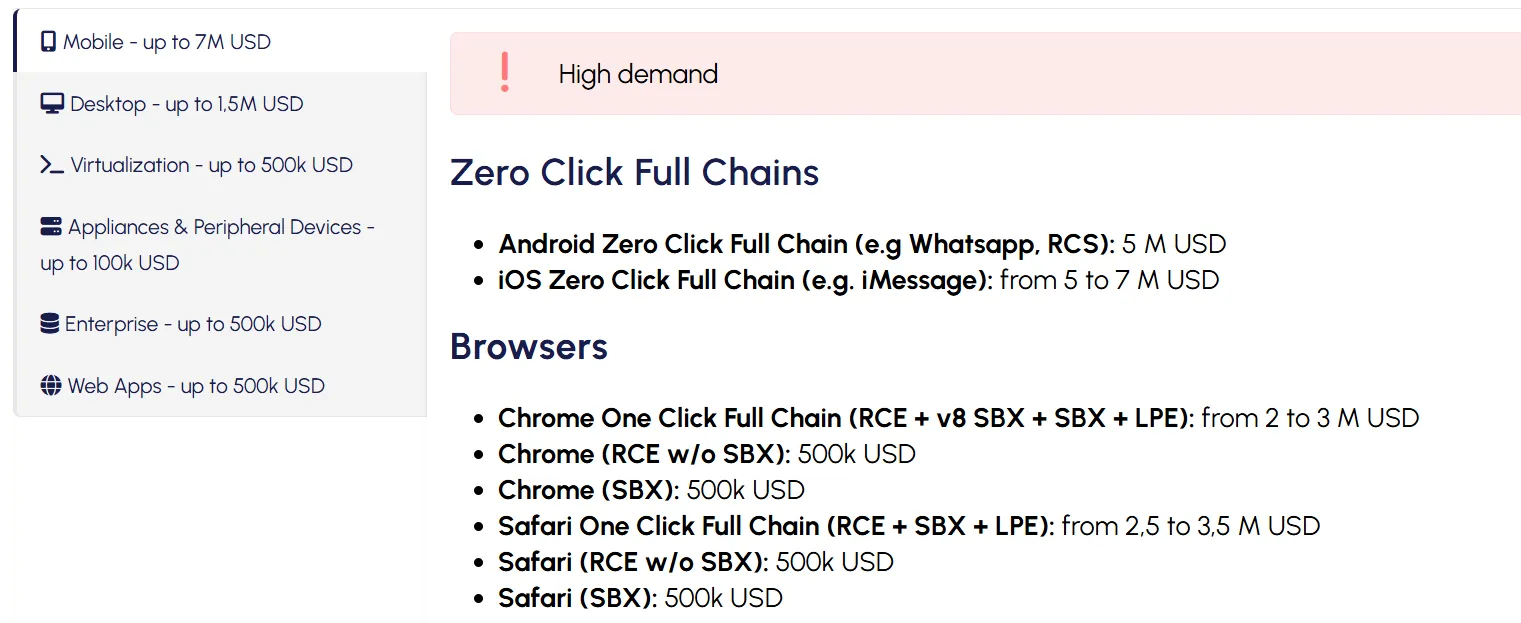
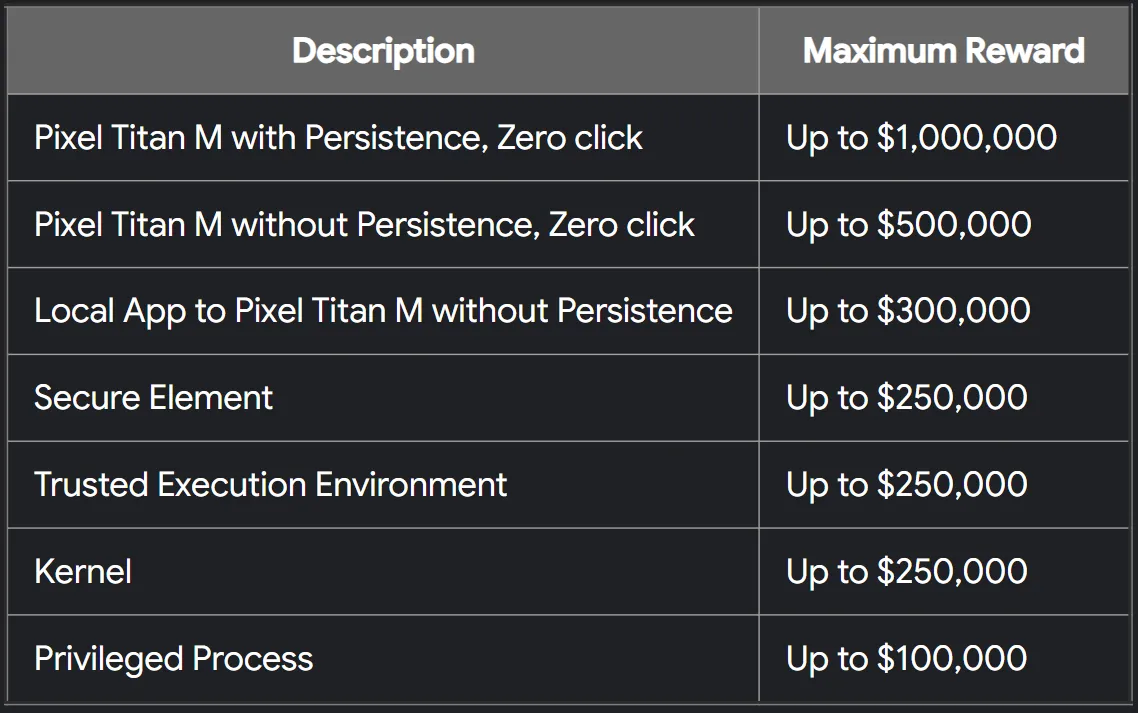
Intermediaries do not notify the vendor, preserving usability for the buyer. That exclusivity lets them write cheques far beyond classic bug bounties from leading software and gadget makers.
In all of 2025 Google’s total bug-bounty payouts reached about $17m. In 2022 the tech giant set a record: $605,000 went to a five-bug Android exploit chain.
In such conditions, security researchers must choose: accept a princely sum knowing an exploit may become a cyberweapon, or work within responsible disclosure.
The biggest name among the “white hats” in this niche is Zero Day Initiative (ZDI). It buys details of vulnerabilities and passes them to Microsoft, Apple or Google, demanding a fix within a set deadline.
ZDI offers up to $1m only for exceptional, highly complex attack vectors during the public Pwn2Own competitions. Day to day, the white broker’s catalogue pays from $500 to $150,000.
Beyond direct payouts, ZDI runs an incentives system ($1 = 1 point). As points accrue over a calendar year, a researcher gains status and a matching bonus.

Thus the 0-day market is bifurcating: high-margin but opaque versus legal yet far less lucrative. The gap is widening.
When weapons migrate to hackers
The market’s central problem is the impossibility of keeping exploits contained. When intelligence officers deploy 0-days, their code can be intercepted, analysed and copied. The tool loses exclusivity and becomes available to groups pursuing simpler, mass attacks.
In spring 2026 two headline cases showed this migration: Coruna and DarkSword.
In March Google Threat Intelligence Group (GTIG) observed use of the Coruna framework, which packed 23 exploits and five full zero-day chains for iOS from versions 13.0 to 17.2.1.
Researchers found that Coruna has direct links to Operation Triangulation, a spying campaign in 2023. The source code was most likely written by a US Department of Defense contractor and later resold via brokers on the secondary market.
Coruna’s subsequent path:
- The framework was used by the hacktivist group UNC6353 (Star Blizzard) for targeted espionage and attacks on Ukrainian users.
- The tool fell into the hands of China-based hackers UNC6691. They planted government-grade cyberweapons on fake cryptocurrency and financial sites. Visiting via Safari silently loaded the PLASMAGRID stealer, opening access to device data, including crypto wallets.
The other case was DarkSword. Attacks ran via malicious websites: visiting them triggered an infection chain on iPhones, granting full device access without the user’s knowledge.
DarkSword’s distribution proved similar: initially it was used by the same UNC6353 group to implant spyware. The framework was later modified with the GHOSTBLADE, GHOSTKNIFE and GHOSTSABER infostealers, geared to pilfer financial data, including crypto wallets.
DarkSword’s lifecycle ended with its leak to GitHub in March 2026. Experts believe the developer firm may have gone bankrupt and tried to monetise leftover code on the grey market, leaving a tool at the level of the NSA in the open for common cybercriminals.
A Bitcoin bug: flaw or feature?
Amid the exploit trade, a natural question arises: is a discovered breach a programmer’s mistake or a deliberately planted backdoor?
Cybersecurity has a concept of “plausible deniability”. It is the guiding principle for professional backdoors. The ideal planted entry point should look like a trivial flaw— a typo, faulty memory handling or a classic buffer overflow. If a researcher finds such a “hole”, the vendor can call it an accident, ship a patch and preserve its reputation. Proving malicious intent in millions of lines of code is nearly impossible.
There are, however, markers that can raise suspicions of a backdoor:
- non-standard cryptography. The use of little-known or weakened cryptographic constants vulnerable to mathematical attacks;
- anomalous logic. Needlessly complex data paths where architecture does not require them;
- obfuscation. Deliberate tangling of code in open-source projects, or supply-chain compromise, when malicious code is injected via third-party libraries.
Closed or partly closed systems such as iOS or Android are often thought to be more vulnerable because of limited transparency. Open-source blockchain projects are sometimes held up as a counterexample. In practice, they offer no guarantees either.
In April 2026 researcher Loïc Morel discovered a computational flaw in Bitcoin’s mechanism.
Under the protocol, the mining difficulty of digital gold is adjusted every 2016 blocks to keep block time near ten minutes. But because of a bug, the timestamp of the last block in the previous period is omitted from the next calculation (it compares 2015 blocks, not 2016).
This gap made a “time-warp” attack possible. If a miner or pool with overwhelming hashrate exploited the flaw, it could trick the algorithm. The system would conclude that mining took longer than it did and dramatically cut difficulty, enabling bitcoin to be mined at an anomalously high pace—up to six blocks per second.
Recent incidents have prompted a rethink of the role of independent security researchers, for whom financial temptation has become a severe test of professionalism and ethics.
Systems are made by humans, so errors are inevitable. While they persist, there will be a market for those who monetise, conceal or even create them.
Рассылки ForkLog: держите руку на пульсе биткоин-индустрии!


